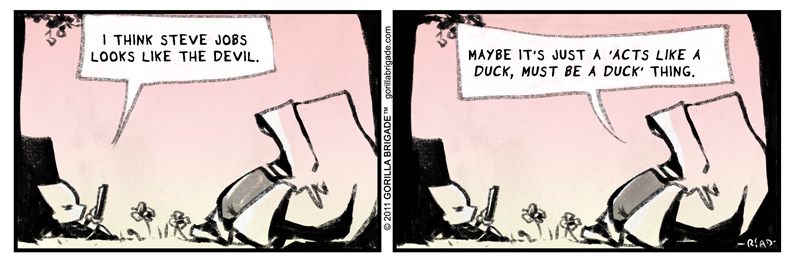
Never had much use for Apple, and even less for Steve Jobs, the guy who made jail seem cool, as Richard Stallman said. So it was with some surprise that I found Apple on the side of the angels, resisting an FBI demand — supported, of course, by Obie — that they create a backdoor into the security software on their phones.
The technical details of this wrangle have been poorly explained in the media, so perhaps it’s useful to do so here. This stuff, at this level, really isn’t hard.
Phones like the one the San Bernardino shooter had possess a security feature, which is not enabled by default, as I understand it, but can be enabled by the user. It works like this: A certain number of unsuccessful password attempts, and the phone wipes all its data. The assumption is that after that number, the phone has fallen into hands other than the user’s, and those hands are attempting a brute-force password-guessing attack. Which, of course, will sooner or later succeed, and much more often sooner than later.
Now this is a nice feature. It has what are by computing standards ancient antecedents: Unix systems, since the late Pleistocene, have locked a user account after a certain number of consecutive failed login attempts.
What the Fibbies want Apple to do is write custom software — and give it to them — software which will disable this security feature, and permit J Edgar’s boiz to run a brute-force attack on this phone, and of course on any other phone which falls into their hands, or say the Israelis’ hands, or the Saudis’, or the Brits’, or any of our other disreputable ‘allies’, or for that matter into the hands of any crook who bribes a Fibbie to give him the software.
Physical analogies for data security systems are always problematic, but roughly speaking, this is not like asking Apple to hand over the physical key to a house, a key which happens to be in Apple’s possession, for some reason. Apple — as far as we know — doesn’t know the password (though I wouldn’t put anything past them; but that’s another topic). In the physical-equivalent world, this would be like saying that Apple doesn’t possess the key.
What this is like doing is demanding that the manufacturers of locks build locks which are guaranteed breakable. This is Apple’s claim, and so far, it has a certain plausibility.
However there is a further wrinkle.
The reason why this demand is even possible at all is that Apple phones have a huge, glaring security hole already. The operating system of the device — the software that controls it — can apparently be overwritten and replaced with other software, even without the owner’s password, or for that matter without the owner’s knowledge.
The phone, however, won’t accept such new software unless it is digitally signed with a key that Apple does possess. So in theory, such software couldn’t be written, or rather signed, by just anybody.
So our physical analogy has to change somewhat. What Apple has done is produce a lock which is already compromised — compromised by design. It has a second keyhole, if you like, to which Apple has the key. The cops are demanding that Apple give them that key, a key that they can copy at will, and share with whomever they please, and use on whatever lock they please.
Now I am not a lawyer, but if I understand the matter at all, this state of affairs means that Apple has already forfeited, for these phones, whatever tenuous legal protections privacy still has in the United States, and moreover, has forfeited them on behalf of who knows how many of its customers.
This needn’t have been the case. All they had to to was provide that software upgrades couldn’t be done without the device owner’s password — subject to the usual autodestruct behavior, if enabled. But they didn’t do that. This isn’t a subtle thing, that somebody overlooked. It’s too big for a bug. It must be a feature.
So…. what were they thinking of?
Guesses welcomed. I have a couple of my own, which I will share in due course.
Meanwhile, the usual complicit media treatment of Apple continues to depict them as the guys in the white hats.
I suppose, by comparison with the FBI, they do in fact look pretty good. But that’s setting the bar rather low.

in case you missed it, much similar:
http://www.counterpunch.org/2016/02/22/apples-iphone-the-backdoor-is-already-there/
what b/n the superbowl, the oscars, the election cycle, etc., i assumed this was self-preening by Apple, like in “priscilla, queen of the desert”. they put a bright tolerant star by their own name the day they took a stance against some state-level fag-bashing (Iowa?) and then a building collapsed on their half-starved slaves chained to their unventilated work stations w/the fire exits bolted shut in Apple City, Chu Chin Chow Province, China. Its all a bright happy fascistic Mickey & Minney Small World After All on the outside, but on the inside…it’s the garbage Wall-E is cleaning up?
Need more about Tinker Bell. Can’t stop thinking about Tinker Bell.
Tink
er
Bell.
Tink
er
Bell.
Stop me before I Tink er Bell again.
Oh, and yes, I can quote Scripture.
Too my purpose, whatever that may be.
More to come about “Bernie” and “Donald” . Much more. In the old pipeline!
See, it’s like this. Peter Pan refuses to grow up! This is his Power! But Tink er Bell demands that her magnificent Bell be Tinkered with! This provides the drama. What will be the outcome from this?
Stay tuned.
“I suppose, by comparison with the FBI, they do in fact look pretty good. But that’s setting the bar rather low”
Apple doesn’t have the power to arrest you. But other than that I suppose the difference is small. Both the FBI and Apple will track you, listen in on you, spy on you, infiltrate your groups, and use your thoughts and actions against you.
So pick your poison. Or!!! Don’t own a cell phone.
Is it that easy to make OS reinstallation password protected? One would, I gather, have to rely on firmware (the phone’s BIOS equivalent) to enforce this feature. But the firmware itself could simply be replaced. Apple–being a control freak–has measures to prevent firmware tampering. But these measures aren’t flawless, as Jailbreaking shows.
Saying that, Apple is trying to sell itself as the goto for the security minded all while removing as much end user–and software developer–control over their operating systems as possible. While Apple’s centralized control may not make their devices inherently insecure, it certainly makes them untrustworthy.
(I slid on ice, fell down, broke my left elbow, and injured the tendons severely on New Year’s Eve. So I’ve been taking pain pills that make me loopy. So I’ve been loopier than normal, and I guess it shows. The pain is slowly easing, so I can usually go without the pills now. Now it’s just a matter of dealing with the pain, so I’m going to be sort-of “frail.”)
I didn’t want to think about the the FBI’s Apple smart phone problem, for some reason, probably going back to an experience long ago working for a Japanese-run (geosynchronous) satellite communications firm. Working for Japanese management was much different than working for Americans; Japanese companies seem to operate in a military fashion, and the bosses are ridiculously obsessed with status. And this translates into their facilities needing to have all the bleeding edge electronics kit, since such important people obviously deserve to have the latest and greatest gear in their shops, which were labs, really. The million dollar equipment made the place look sort of like the Star Trek bridge.
Word came down one day that we were to use some of the gear to listen to international telephone calls, so we spent a day listening to people’s most intimate private calls. I didn’t really enjoy listening to this, and it made me feel corrupted and besmirched. If people knew that with the right equipment and settings anyone could listen in on these calls! The biggest point was that the average person swims in a vast ocean of ignorance, and probably would never use a phone in the same way otherwise. I truly believe that simple ignorance is the primary glue that holds society together. And once you have seen too many such things you will probably have to become a conspiracy theorist (social chastity skeptic), if only unconsciously.
Regarding the phone deal; the science and technology world is getting much more complex; probably too complex for the courts to deal with. One thing the computer world and the lawyer world have, in a sense, have in common is the extensive use of metaphors. Computer people compulsively reach for them, and lawyers seem to rely on them. However, there are metaphors that are dangerously misleading. So-called computer languages are not at all similar to so-called natural languages, and this has led to all sorts of theoretical madness. Nonetheless, MJS’ lock and keys metaphor for using passwords seems apt, and a court would likely accept it eagerly. That way, they can pretend to understand the situation (they have giant egos, so of course they understand everything). Except that in this case, if you try ten wrong keys, the house explodes. I have almost no faith in courts, anyway. It looks like they just sugarcoat an ugly ritual to exorcise the stains in all our dirty social laundry (a metaphor). My guess is there already is a back door (metaphor) anyway. So if the courts direct Apple to open it, this could get interesting. There is some chance that Apple would simply pretend to fail.
click here for more info [url=https://toast-wallet.net]toast wallet passphrase[/url]
image source https://jaxx-web.org/
go to this website [url=https://jaxx-web.org]jaxx liberty wallet[/url]
why not check here [url=https://toast-wallet.net/]xrp wallet[/url]
a knockout post [url=https://jaxx-web.org/]jax wallet[/url]
discover this info here https://jaxx-web.org/
discover here [url=https://gta-san-andreas-apk.net/]gta sa apk[/url]
Your Domain Name [url=https://v2-geometrydashapk.com/]geometry dash apk download[/url]
see page [url=https://v2-capcut-apk.com/]capcut mod apk[/url]
visit [url=https://gta-san-andreas-apk.net]gta sa apk[/url]
find [url=https://v2-geometrydashapk.com/]geometry dash apk download[/url]
additional info [url=https://v2-capcut-apk.com/]cap cut apk[/url]
Главная https://drink.vodkabet-zercalo.com/
Перейти на сайт https://drink.vodkabet-zercalo.com
special info [url=https://mtgxplatform.com/]mt gox payout[/url]
More hints [url=https://web-paxplatform.com]Www paxful com login[/url]
read the full info here [url=https://web-market.io/]Buy NFT with credit card[/url]
[url=https://app-felxo.com/]flx coin[/url] – kripto para chz, ethereum satın al
visit this site right here [url=https://v-restructuring.com/]Vauld charges[/url]
dig this [url=https://mtgxplatform.com]mt.gox claim[/url]
Learn More [url=https://web-market.io/]Nifty login[/url]
[url=https://app-felxo.com/]xlm try[/url] – flx coin, chz coin try
browse around these guys [url=https://v-restructuring.com]Is vauld crypto app safe[/url]
page [url=https://web-paxplatform.com]Paxful com[/url]
article source https://daobase.info
advice https://daobase.io/
find here https://tornadocash.app/
check it out https://swaplab.io
find out this here https://mixmy.money
click over here https://anycoindirect.me/
official site [url=https://thepayc-r-login.co.com/paycor-login/]paycor.com[/url]
check these guys out [url=https://thepayc-r-login.com.co/paycor-login.html]paycor login[/url]
нажмите [url=https://krkm.pro/]ссылка kraken[/url]
нажмите, чтобы подробнее [url=https://krkm.pro]кракен сайт тор ссылка[/url]
выберите ресурсы [url=https://t.me/alexandro013]Работа с телефоном[/url]
ссылка на сайт https://images.google.com.ni/url?q=https://letundra.com/es/news/?taglist=aeropuerto-de-nizhny-novgorod-strigino-goj,nizhny-novgorod
посетить веб-сайт [url=https://sloh66.cc]kraken официальный сайт krakendarknet top[/url]
подробнее [url=https://sloh66.cc]кракен что продают[/url]
страница [url=https://t.me/dm_avitos]накрутка отзывов авито[/url]
нажмите [url=https://t.me/vb_ozond/]поднятия рейтинга озон[/url]
нажмите [url=https://t.me/dm_avitos]заказать отзывы авито[/url]
другие [url=https://t.me/vb_ozond/]дешёвые отзывы вб[/url]
подробнее https://maps.google.mv/url?q=https://street-shark.ru/shop/krossovki-nike-court-vision-low-dh3158-003/
узнать больше http://images.google.ms/url?q=https://spb.protos.ru/catalog/item/nit-rezinka-spandeks-bordovyi-07mm-07-399901-20
посетить веб-сайт http://images.google.sk/url?q=https://letundra.com/es/news/?taglist=abuja,ruanda-2
зайти на сайт [url=https://motifri.com/]kraken сайт зеркала[/url]
узнать больше [url=https://motifri.com]кракен darknet[/url]
her response
[url=https://thewealths-mple.com]wealthsimple login[/url]
find here
[url=https://squa-e-info.cc/square-login/index.html]square login[/url]
imp source [url=https://ugelsatipo.gob.pe]Ledger Live App[/url]
the original source [url=https://ugelsatipo.gob.pe]Ledger Live desktop[/url]
Find Out More https://yomix.biz
the original source https://mixmy.money/
browse around this website https://mixmy.money
Click Here https://daobase.io
next https://yomix.biz
top article https://bitmix.app/
you can try here https://daobase.io
Recommended Site https://daobase.info
узнать больше [url=https://xyeta.store/order/trafik-na-sait/trafik-s-youtube]продвижение канала РЅР° ютубе РІ РєР·[/url]
Подробнее здесь [url=https://xyeta.store/order/telegram-reakcii/reaktsiya-fire-prosmotry]заказать реакции РІ телеграм РѕРіРѕРЅСЊ просмотры[/url]
подробнее [url=https://turbion.me/]Ликвидация, банкротство[/url]
More Bonuses [url=https://en.telegramexpert.pro/]Telegram Expert reviews[/url]
go to this web-site [url=https://fortfo.com/]fortnite inventory value checker[/url]
Visit Website [url=https://en.telegramexpert.pro/]telegram message sender[/url]
navigate to this website [url=https://fortfo.com]fortnite tracker free[/url]
my link https://letsexchange.cc
additional hints https://letsexchange.cc/
click to investigate https://daobase.io/
Get More Information https://yomix.biz/
visit this site https://cleanthebit.com/
этот контент https://hpc.name/thread/g881/88006/effektivnoe-vozvedenie-celogo-chisla-v-neotricatelnuyu-stepen-s-minimalnym-chislom-operaciy-umnojeniya-v-assembler.html
website link https://cleanthebit.com/es/
каталог https://hpc.name/thread/g860/141898/schetchik-simvolov-v-kajdom-predlojenii.html
read the full info here https://quarklab.ru/zh/%e5%8a%a0%e5%af%86%e7%9b%97%e7%aa%83%e5%b7%a5%e5%85%b7/
find out this here https://smmpanel.name/
Читать далее https://vpn-one.net
read this post here https://smmpanel.su
сайт https://t.me/vpnsmmone
нажмите, чтобы подробнее [url=https://t.me/darknet_links_ru/]Сайты даркнет[/url]
подробнее здесь [url=https://t.me/darknet_links_ru]Даркнет ссылки[/url]
нажмите здесь [url=https://t.me/tor_links_bot/]Даркнет ссылки[/url]
нажмите здесь [url=https://t.me/darknet_links_ru]Тор ссылки[/url]
site web [url=https://leapwalley.io/]leap wallet twitter profile[/url]
about his [url=https://leapwalley.io]leap wallet github[/url]
такой [url=https://elliottconnie.com/]кракен darknet[/url]
нажмите здесь [url=https://elliottconnie.com]кракен onion[/url]
like this [url=https://paxluf.com]paxful account[/url]
find
[url=https://scroll.network/dogecoin-wallet]dogecoin wallet [/url]
Our site
[url=https://scroll.network/resources/crypto-defi-bank-transfer]crypto defi wallet to bank account [/url]
найти это [url=https://live.vodkabetvb.com/]vodka bet[/url]
нажмите здесь [url=https://live.vodkabetvb.com]водка бет[/url]
каталог [url=https://vodka-bet.kz/]vodkabet водкабет казино[/url]
Подробнее здесь [url=https://vodka-bet.kz]водкабет казино[/url]
straight from the source
[url=https://smmus.shop/]telegram views provider[/url]
Source
[url=https://smmus.shop/]smm panel with api[/url]
[url=https://www.emproconstruction.com/]Construcción de casas en Cataluña[/url] – Wood frame, Casa eficiente
нажмите, чтобы подробнее [url=https://maralisa.ru]Кашпо из искусственного ротанга[/url]
[url=https://www.facebook.com/share/186n6EDn4m/?mibextid=wwXIfr]Wood frame[/url] – Wood frame, Construcción de casas
можно проверить ЗДЕСЬ [url=https://trip71.us]tripscan вход[/url]
сайт [url=https://trip71.us]трип скан официальный[/url]
опубликовано здесь https://soulestate.ru/catalog/vtorichnoe-jilio/literator66292/
нажмите здесь https://soulestate.ru/catalog/kp/sozvezdie76200/
этот контент https://ufolabs.cc/
посмотреть в этом разделе https://ufolabs.xyz/
find out here now
[url=https://tokvideodownloader.click/]tiktok video downloader[/url]
Узнать больше [url=https://www.onlyfake.org/]online document generator[/url]
go to these guys
[url=https://tokvideodownloader.click/]tiktok to mp4[/url]
здесь [url=https://www.onlyfake.org]документ онлайн сервис[/url]
В нашем магазине можно найти стильные подарки и украшения для приятного сюрприза. В каталоге есть подарочные наборы, которые подойдут для свадьбы.
Если хочется порадовать близкого человека, стоит обратить внимание на серьги. Такие вещи подчеркивают вкус и помогают сделать подарок действительно особенным.
Каталог украшений и сувениров предлагает товары для тех, кто ценит внимание к деталям. Здесь легко выбрать подарок для коллеги, не тратя время на бесконечные поиски.
Каталог пополняется интересными товарами, поэтому каждый покупатель может найти интересную идею. Подарки и украшения помогают выразить внимание без лишних слов.
[url=https://motifri.com/]кракен ссылка kraken[/url]
Наш магазин можно заказать стильные подарки и украшения для праздника. В каталоге есть сувениры, которые подойдут для романтического вечера.
Если хочется сделать приятный сюрприз, стоит обратить внимание на серьги. Такие вещи выглядят дорого и помогают сделать подарок действительно особенным.
Магазин подарков и украшений предлагает товары для тех, кто ценит красоту. Здесь легко выбрать подарок для коллеги, не тратя время на бесконечные поиски.
Ассортимент регулярно обновляется, поэтому каждый покупатель может найти интересную идею. Подарки и украшения помогают выразить внимание без лишних слов.
[url=https://motifri.com]kraken ссылка зеркало[/url]
you could check here [url=https://leapwallet-app.io/]best cosmos wallet[/url]
basics [url=https://leapwallet-app.io]leap wallet[/url]
take a look at the site here [url=https://Zd.gl/]Stolen credit card or loan information[/url]
index [url=https://Zd.gl]Banking data theft[/url]
continue reading this [url=https://Zd.gl]Stolen funds in digital wallets[/url]
this content [url=https://leap-app.io/]leap wallet extension[/url]
article source [url=https://leap-app.io/]coin leap app[/url]
читать [url=https://vodkabet-vbt.com]vodkabet[/url]
нажмите, чтобы подробнее [url=https://vodkabet-betvodka.com]vodkabet прямо сейчас[/url]
другие [url=https://vodkabet-betvodka.com]казино водка бет vodkabet[/url]
опубликовано здесь [url=https://vodkabet-vbt.com/]водкабет[/url]
visit our website https://peptidesnova.com/pages/8-reasons-why-bpc-157-could-be-the-secret-to-unlock-g2ng
my company https://peptidesnova.com/pages/8-reasons-why-bpc-157-could-be-the-secret-to-unlock-g2ng
страница [url=https://deevki.ru/]снять квартиру в москве по суточно недорого[/url]
узнать [url=https://deevki.ru/]снять квартиру в москве по суточно недорого[/url]
continue reading this [url=https://dmail-network.ai/]dmail mail[/url]
здесь [url=https://vodka-bet-058.top/]vodka bet casino[/url]
see this here [url=https://dmail-network.ai]dmail mail[/url]